How to Exploit 6 Common Network Services
Spoiler free walkthrough of TryHackMe's Network Services 1&2 Rooms
Prefer to watch this article instead? No Problem!
Today we are going to do a spoiler free walkthrough of the three challenges that make up the network services one and network services two in the TryHackme module, Network Exploitation Basics. We're gonna learn how to exploit Telnet, SMB, FTP, smtp, nfs, and MySQL using the MITRE ATT&CK matrix. If you can research the ATT&CK technique, then you'll be able to get a hint of what to do next if you're stuck without knowing the specific answer.
For those threat hunters out there, or offensive security professionals that eventually want to become leaders in the cyberspace. Stay tuned until the end of the episode to discover the root cause ATT&CK steps in each of the challenges
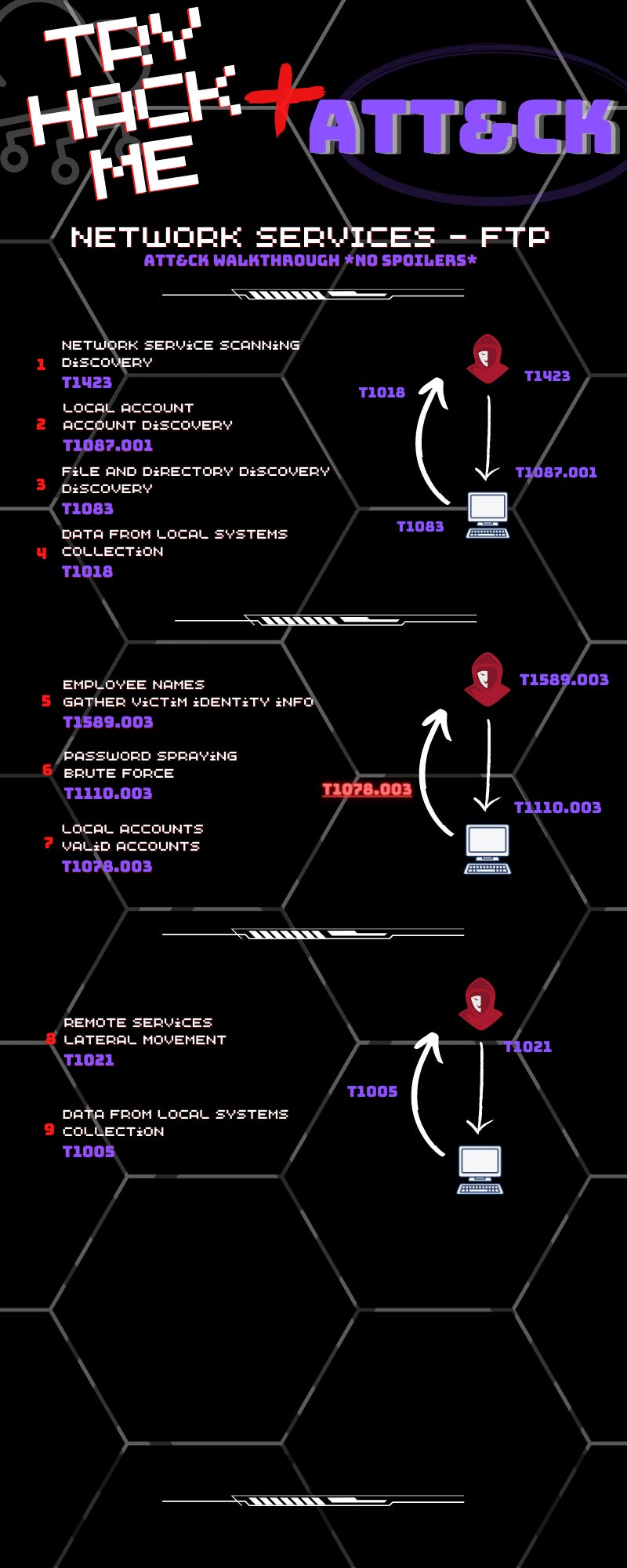
if you look on the graphic, you'll see each of the MITRE ATT&CK, TTPs, and if you research those, you'll get a rough idea of what you're supposed to do.
SMB
Okay, first up is going to be smb. SMB is done in 10 steps, 10 MITRE ATT&CK steps. The first step is the network service scanning. So from the ATT&CK box we're gonna scan something. The second step after that is to discover a network share.
We're gonna scan something and then we're gonna discover a network share. Step three is SMB share remote services. So we're gonna do something with the share that we discovered, which is gonna result in step four data from local systems, which is part of collection. So we scan, we discover an open share, we do something with the open share.
We collect something that leads to step five, which is local account discovery, local accounts. And with this local account that we discover, we're going to move into file and directory discovery, which results in step seven, which is private keys, part of unsecured credentials. So we scan, find a share, do something with share.
Collect something from the box. We discover a local account. We use that account to do another file and directory discovery, and we discover some private keys, which leads to the final phase, local accounts. Step eight, we discover an account. We use that account to SSH and from our SSH shell, we collect data from the local system, right?
So we're just doing data collection there. So the SMB portion of network services one in 10 steps.
Telnet
Okay. Next step is Telnet. And Telnet is, we do that in nine MITRE ATT&CK steps. So steps one, pretty much like all of these since it is part of the network challenges. We're gonna do network service scanning, so we're gonna discover something. But in this time, this step is local account discovery.
So we scan and we discover something which results in step three unix shell, which is part of the command and scripting interpreter technique. So that's a pretty quick jump from just scanning a box to now we have a unix shell . So we're gonna, step four is we're going to do remote system discovery.
So step three, Unix shell command and scripting interpreter. Step four, remote system discovery, if you can kind of infer as to what to do there. Step five, we're gonna stage some capabilities. We're going to, upload malware. Step six, we're going to Unix Shell again, command and scripting interpreter. Step seven
there's gonna be a command and control channel established back to our attack box. So we scan, we immediately find a local account. We can use that account to do unix shell command and scripting interpreter. We discover some, maybe some network comms. We stage some capabilities as the attacker.
We go back to the Unix shell, and next thing you know, there's an encrypted command and control channel. Talking back to our box now from that encrypted channel, step eight, we are going to exfil over c2, which is step nine. So that was Telnet and nine steps.
FTP
Now the last part of network services one is ftp. So again, network service scanning.
We're gonna scan it up. And we're going to discover a local account, which is great. And from that, with that account, we go to step three, which is file and directory discovery. And then we collect some data from the systems. So we scan it, we discover an account, we discover some files on the target, and we collect something.
Moving into phase two, we're gonna be able to gather some victim identity info. The employee names. And with these employee names, we're gonna be able to do some stuff like step six, password spraying. Now after step six is step seven, local accounts. Valid accounts. So between step six and seven, I think you'll be able to, with that, without having a spoiler, you can figure out what's going on.
You know what you have to do, but you don't know exactly how to do it. And when I was going through and learning stuff, I always found that really helpful. Those were the best hints, the ones that told me what I needed to do, but not how to do it. Now, after we get a valid account, guess what? We can use remote services to do lateral movement.
Boom. Step nine. Data from local systems. And those were the three challenges that were part of Network Services. One.
Root Causes Network Services 1
Now at the beginning of the video I talked about the root cause, TTPs, right? If we go back and look at the graphics in the video, in each of the steps, there was always one TTP that was highlighted in red.
Let's go back and take a look at that. Okay, so for SMB, the TTP that was highlighted in red was step three. SMB shares remote services. Now, if the threat hunters or the people that want to figure out the root causes of these ATT&CKs by focusing on these root cause TTPs and how to defend it against them, it could be really cool, like you figure out how to stop the attack at the earliest possible time where you can stop the attack.
So for SMB, that would be the SMB share's part. Stopping step three would significantly reduce the attack surface of SMB, of the SMB challenge for Telnet. That is also step. Three, which is the Unix shell. It's a Unix shell command and scripting interpreter. There is something with this step that if it was configured a little bit differently, that is the way that this attack would be stopped.
A lot of the, a lot of the other things that were in here, pretty much from step three forward, they all require that initial access of step three to Unix show. And for FTP, Let's see, what do we got here? The root cause ATT&CK, TTP is step seven local accounts.
Valid accounts. Now there's something, if you look at, the previous step. It's not so much that the password spraying or the brute force is the root cause. It's why it worked is the root cause. So being able to address those low complexity accounts or those things those accounts that have maybe issues with passwords or easily guessable, that's truly the root cause for this ATT&CK.
Everything else was if you go up to step three, you might say what about being able to. The files and directories. You may need those for customers, right? So that's not really the root cause. The root cause is having terrible credentials.
SMTP
Network Services 2
Okay, first up is SMTP. SMTP is done in six steps. It's actually pretty quick. First, like all of the step ones in network services one and two, we're gonna do network service scanning. We're gonna scan the victim host, and we're gonna discover something. Now, part two or step two is we're gonna gather victim identity info, which is part of reconnaissance, and we're gonna discover step three, default accounts, valid accounts.
So we're gonna scan something phase one, we're gonna scan something, we're gonna get some identification info, and we're gonna discover some default accounts. Step four is we are going to do password spraying, which is part of brute force, which eventually ends up in an SSH remote shell or an SSH shell.
And step six, we just collect the flag from the box. That's actually really quick. It was so quick that I had to put a big graphic because there was no phase three. It was only phase two.
NFS
Okay, next up is NFS. Step one, scan it. We're gonna scan it up. We're gonna step two, discover some victim host information.
Step three, we're gonna discover a network share. And step four, from that shared drive, we're gonna collect some data. So scan, discover some information discover a share, network share. And we're gonna collect some stuff from it. Okay? Phase two, we are going to find some private keys. Does that come from step four, or is that step five?
You'll just have to find out. So we're gonna do private keys, which we're gonna turn into step six, which is ssh. So we're gonna take the private keys in ssh. We have a local account now, right? Because we're SSHing with a valid account. But here's where the fun part comes. We're gonna take that valid local account and we're gonna taint some shared content.
Now, this one was actually difficult to map. to MITRE ATT&CK, but I do think that this one is T1080 taint shared content. If you really look into it and read about the technique it's gonna give you, I feel where you need to go to complete this box. Phase three is step nine, SetUID and SetGID.
So we're gonna abuse some elevation. We're gonna abuse some ways that the elevation control was set up. Now, step 10, we're gonna SSH back in, which leads to step 11. Exploitation for privesc, right? You know the steps, but you may not know. Does nine? Lead to 10 does 10 lead to 11? Or does nine set up 10? You'll have to find out on your own.. But anyway, once we SSH in we are privilege escalated at that point and we can collect data from the victim host, which is the flag.
MySQL
And the last one, MySQL and that is eight MITRE ATT&CK steps. Step one, we're gonna scan it up. Stage two, we're gonna stage capabil.
So we scan something up and we're like, You know what? We need to stage some capabilities. And step three is we're gonna find default accounts, valid accounts, phase one, phase two, automated collection. So we're gonna collect some stuff. Now, automated pretty much signifies a tool, right? You're not manually collecting things that would be manually.
This is automated, so we're gonna automate it, collect some, Which leads us to step five, which is credential from a password store. So what are we collecting in step four? I don't know, but step five is credential from a password store. Step six. Yeah, obviously we found a credential from a password store, so we're gonna crack it.
So step six is we're gonna crack the password, which leads us to step seven and phase three, which is ssh. And we SSH to the victim host, and we collect data from the victim, which is the flag. So that was my sequel in eight steps. And you scan, set something up on your box stage capabilities. You're gonna find some accounts, you are going to do some automated collection, you're gonna find some passwords somewhere.
You're gonna crack those passwords. You're gonna use that to ssh into the box and then collect the flag.
Root Causes SMTP, NFS, MySQL
If you remember at the start of the video, I mentioned that each of the challenges would have a root cause, ttp. So let's go back through and look at what those are.
That will be highlighted in red.
Okay. Root cause. TTP for SMTP challenge is step four. Password spring brute force.
The reason I chose password spraying brute force is really because it's was a little bit difficult to map things like poor credential hygiene to MITRE ATT&CK. You can get some things, but not all of 'em. So just the fact that being able to password spray and brute force and account. Is means that somebody should be, doing some better credential hygiene.
So if you were not able to password spray the, you wouldn't be able to steal the the flag, right? You can still have some default accounts in step three, you can't really stop reconnaissance, but what you can stop is people from just guessing the password, going down to nfs. We are going to see that step eight taint shared content, which is part of lateral movement, is the root cause here.
So that's really far down. Now, the reason I put it so far down was because thinking from a business standpoint, which is why, one of the reasons why we're going through the MITRE ATT&CK , like we're mapping it to MITRE ATT&CK, this NFS server may exist for customers and if you shut down, Like from step three up, you may limit the business capabilities of this device.
Now, however, there was a significant misconfiguration in step eight, and by stopping that you prevent all of the other things that happen later on.
And again, that is from the mindset of a cybersecurity professional, thinking about the business and going down to MySQL, the root cause, TTP for that is step three, default accounts, valid accounts. The people just left the default accounts up and they left the default accounts privileged and that just caused the attack.
So just that one was actually really early on. It doesn't need to be there. And it enabled all the other things that were further down.
So thank you for watching. Don't forget to like and subscribe to get notified when other spoiler free walkthroughs come out either for TryHackMe or HacktheBox or any other thing that I can get my hands on to teach spoiler free steps and also how to map it to business impact cuz that's important to cyber security doesn't make money, so you have to be able to show how what you're doing saves money.
Thanks!